TL;DR:
- Forensic data recovery involves evidence preservation, detailed documentation, and specialized techniques beyond standard tools. It is essential for legal, compliance, and critical personal situations where data integrity and chain of custody are paramount. Local experts in Los Angeles provide expert, hardware-level solutions tailored to the complexities of Apple devices and encrypted storage.
Most people assume that if they accidentally delete a file or their Mac crashes, a quick download of a recovery app will solve the problem. That assumption is dangerously wrong, particularly for Apple device owners in Los Angeles dealing with serious data loss. Forensic data recovery is a fundamentally different discipline from the consumer tools you find with a quick internet search. It preserves file integrity, maintains documented evidence chains, and navigates encryption systems that would stop standard software cold. Understanding the distinction between ordinary recovery and forensic-grade methods can mean the difference between retrieving your critical data and losing it permanently.
Table of Contents
- Understanding forensic data recovery
- Core forensic data recovery methodologies
- Challenges with Apple devices: encryption, SSDs, and secure deletion
- When and why Los Angeles residents need forensic data recovery
- Our expert take: What Apple users in Los Angeles miss about forensic recovery
- Connect with Los Angeles forensic data recovery professionals
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Forensic recovery preserves evidence | Unlike standard recovery, forensic techniques maintain data integrity for legal or regulatory use. |
| Apple devices require expert methods | Secure deletion, SSDs, and hardware encryption make Apple recovery complex and best handled locally. |
| Method choice impacts success | Logical, physical, and filesystem approaches have unique strengths and limits for various scenarios. |
| Local expertise ensures compliance | Los Angeles providers understand relevant laws and work fast for Apple device owners facing urgent data loss. |
| DIY tools often fall short | Consumer-grade solutions risk altering evidence and can’t always recover from encrypted or securely deleted drives. |
Understanding forensic data recovery
Having set the context, let’s clarify what forensic data recovery really means and why it’s distinct from ordinary approaches.
Forensic data recovery is not simply about getting files back. It is a structured, evidence-focused process designed to retrieve data while preserving the original state of the storage medium as completely as possible. Every action taken during a forensic recovery is logged, verified, and documented, creating an audit trail that can hold up to scrutiny in legal proceedings, compliance audits, and corporate investigations. This is fundamentally different from running a consumer utility that writes temporary files to your drive, potentially overwriting the very data you need.
The scenarios where forensic recovery becomes essential are broader than most users recognize:
- Legal disputes involving employment termination, intellectual property theft, or civil litigation often require verified file metadata and timestamps.
- Compliance audits in regulated industries such as healthcare, finance, and law require documented proof that data was handled correctly.
- Corporate investigations into insider threats, fraud, or data breaches demand that evidence not be contaminated by careless recovery attempts.
- Personal situations such as estate settlements or custody disputes may require professionally recovered files that retain their original integrity.
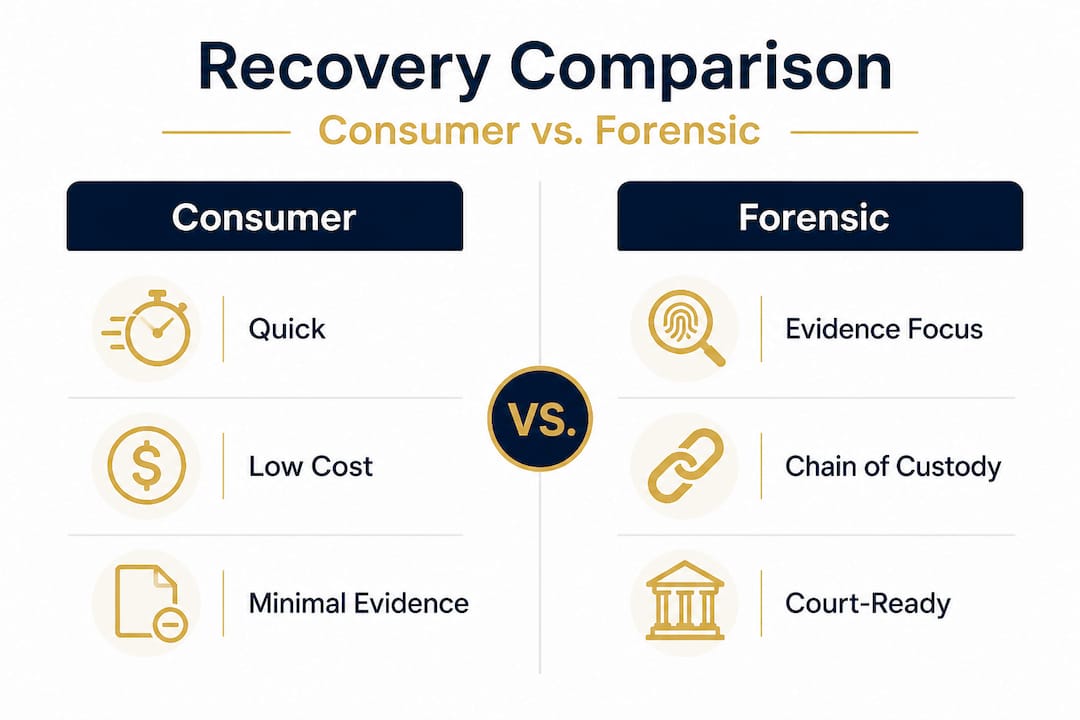
The core distinction between consumer-grade and forensic-grade recovery lies in methodology. As forensic acquisition methods describe it, logical acquisition uses OS APIs to access data that is currently visible; physical acquisition creates a bit-for-bit copy of the entire storage medium including deleted space; and filesystem acquisition targets specific partitions or volumes. Consumer tools typically perform a simplified version of logical acquisition only, which means they miss deleted data, damaged partitions, and hidden file structures entirely.
“Forensic recovery is not about speed. It is about certainty. Every byte recovered must be accounted for, and every step must be defensible.”
For anyone working with a hard drive data recovery overview on a Mac, understanding these distinctions before taking action is critical. Reaching out to data recovery services in Los Angeles that specialize in forensic methods ensures your data and its legal defensibility remain intact.
| Feature | Consumer recovery tools | Forensic recovery methods |
|---|---|---|
| Evidence preservation | Minimal or none | Full chain of custody |
| Data alteration risk | High | Minimized through imaging |
| Handles encrypted drives | Rarely | Yes, with hardware expertise |
| Legal admissibility | Not applicable | Verified and documented |
| Deleted file recovery | Limited | Extensive, physical level |
| Cost and speed | Fast and affordable | Slower and more thorough |
Core forensic data recovery methodologies
Now that we know forensic recovery is evidence-focused, let’s dig into the specific methods experts use for Apple devices.
The three primary forensic acquisition methodologies each serve distinct purposes depending on the condition of the device, the type of data needed, and the legal requirements attached to the case. Choosing the wrong method can reduce recovery chances or compromise evidence quality.
Logical acquisition is the starting point for most forensic examinations when the device is undamaged and accessible. It accesses the operating system’s file management layer using native APIs, collecting files that the OS recognizes as present. This is relatively fast and less invasive, but it has a significant limitation: it cannot see data that the filesystem no longer indexes, including deleted files or data in unallocated storage space. For Apple devices running macOS with APFS (Apple File System), logical acquisition can retrieve active files and some volume metadata, but it stops short of anything the system has marked for deletion.
Physical acquisition is far more intensive. It creates a complete, sector-by-sector duplicate of the storage medium, capturing everything from active files to deleted remnants, swap space, and unallocated clusters. On traditional spinning hard drives, this is a reliable process. On Apple’s soldered SSDs, physical acquisition becomes substantially more complex because the chips are integrated directly onto the logic board, often requiring specialized hardware interfaces and, in some cases, chip-off procedures where NAND memory is physically removed and read independently.
Filesystem acquisition targets a specific partition or APFS volume rather than the entire physical drive. This is useful when only one section of a multi-partition setup is relevant to a case, or when partial drive damage limits access to a specific volume.
Here is how to think about which method applies in different Apple device scenarios:
- Healthy MacBook with intact OS and accessible files: Logical acquisition is appropriate for speed and reduced invasiveness.
- MacBook with failed logic board but intact SSD: Physical or chip-level acquisition is required, often involving board-level repair first.
- iMac with formatted drive: Physical acquisition is necessary to recover data from unallocated space.
- Mac with APFS volume corruption: Filesystem acquisition targeting the affected volume, combined with snapshot analysis, may yield the best results.
- Mac Mini used in a corporate setting with FileVault encryption: Physical acquisition combined with decryption key handling and board-level access is required.
Pro Tip: Never run Disk Utility’s First Aid or any third-party repair tool on a drive that may contain forensically relevant data. These operations write to the drive and can permanently overwrite deleted data that only a physical acquisition would have captured.
For specific guidance on MacBook Pro forensic recovery, or to learn about proven Mac recovery methods used across different scenarios, Macwest has documented detailed approaches for Los Angeles clients. Businesses relying on networked storage should also be aware that NAS recovery for Macs involves its own set of forensic considerations tied to RAID configurations and volume integrity.
Challenges with Apple devices: encryption, SSDs, and secure deletion
Understanding the technical methods, we must also recognize the practical challenges Apple devices create for forensic recovery.
Apple has built some of the most sophisticated security architectures in consumer computing, and those same protections that keep your data safe from hackers create serious obstacles for forensic recovery specialists. The challenges are not theoretical. They are the daily reality for anyone attempting to retrieve data from modern Mac hardware.
The most significant obstacles include:
- T2 and M-series chip encryption: Apple’s T2 security chip and all M-series Apple Silicon processors tie encryption keys directly to the hardware. This means the encrypted SSD from a failed MacBook cannot simply be removed and read in another machine. As T2/M-series encryption demonstrates, the encryption keys are bound to the specific board, requiring board-level repair or specialized techniques to access data even with the correct credentials.
- SSD TRIM commands: TRIM is a background process that tells the SSD controller to securely zero out blocks that have been marked as deleted by the filesystem. On Apple SSDs, TRIM runs aggressively, which means that data the filesystem deleted may be physically overwritten within minutes or hours, reducing recoverability significantly compared to traditional spinning hard drives.
- Secure overwrite and Secure Empty Trash: When a user performs a secure deletion or when macOS triggers secure overwrite during certain operations, the data is deliberately scrambled before the blocks are released. Standard forensic imaging cannot recover data from securely overwritten sectors.
- APFS snapshots as a recovery opportunity: Not all Apple-specific features work against recovery. APFS, introduced with macOS High Sierra, creates point-in-time snapshots that can roll back data to earlier states. A skilled forensic technician can locate and mount these snapshots to retrieve files that were present before a deletion event, providing a meaningful retrieval path on otherwise clean-looking drives.
Pro Tip: If your Mac has experienced sudden failure and you suspect data loss, power it off immediately and do not attempt to restart it. Every boot cycle on a failing drive or SSD can trigger TRIM operations and overwrite the very data you need recovered.
The board-level repair requirement for encrypted Apple devices is one area where local Los Angeles expertise matters enormously. Shipping a Mac to a distant service center introduces delays, shipping risks, and chain-of-custody concerns. For a thorough understanding of Mac data recovery challenges specific to Apple hardware, working with a local team that has direct experience with T2 chip bypass, NAND access, and logic board micro-soldering is the most reliable path forward.

When and why Los Angeles residents need forensic data recovery
Technical barriers aside, many Los Angeles users wonder whether they need forensic recovery or standard solutions.
The answer depends heavily on the context of the data loss and what you plan to do with the recovered files. For someone who accidentally deleted vacation photos from a functioning MacBook, a standard logical recovery may be sufficient, assuming TRIM hasn’t already cleared the data. But the moment data loss intersects with legal, financial, or business-critical situations, the standard recovery approach becomes inadequate and potentially harmful to your case.
Here are the most common scenarios where Los Angeles residents and businesses need verified forensic recovery:
- Employment litigation: Wrongful termination, harassment, or discrimination cases often hinge on email records, document timestamps, and communication logs that must be verified by a forensic expert.
- Business disputes: Partnership dissolutions, contract breaches, or theft-of-trade-secrets cases require electronic evidence that demonstrates authenticity and unbroken chain of custody.
- Regulatory compliance: Healthcare providers under HIPAA, financial firms under SEC regulations, and legal practices under state bar requirements must demonstrate that data was handled, stored, and recovered according to specific standards.
- Insurance claims: Proving the existence and content of files lost in a disaster, theft, or accidental deletion sometimes requires forensic-grade documentation that consumer tools cannot provide.
- Incident response: After a cyberattack or ransomware event, forensic recovery helps identify what data was accessed, altered, or exfiltrated, information critical for breach notification requirements.
“The difference between recoverable evidence and lost data often comes down to the first decision made after the loss event. Choosing the right recovery approach from the start protects both the data and the legal case.”
Consumer tools are fast but non-forensic. They do not create verified images, they do not log their actions, and they frequently write to the source drive during operation. Professionals use verified imaging workflows that are slower and more costly but produce results defensible in any legal or compliance context. For Los Angeles residents evaluating their options, the best Los Angeles recovery service combines technical capability with an understanding of California’s specific legal landscape. For businesses managing large storage arrays, RAID and HDD recovery in Los Angeles adds another layer of forensic complexity that requires dedicated infrastructure and expertise.
Our expert take: What Apple users in Los Angeles miss about forensic recovery
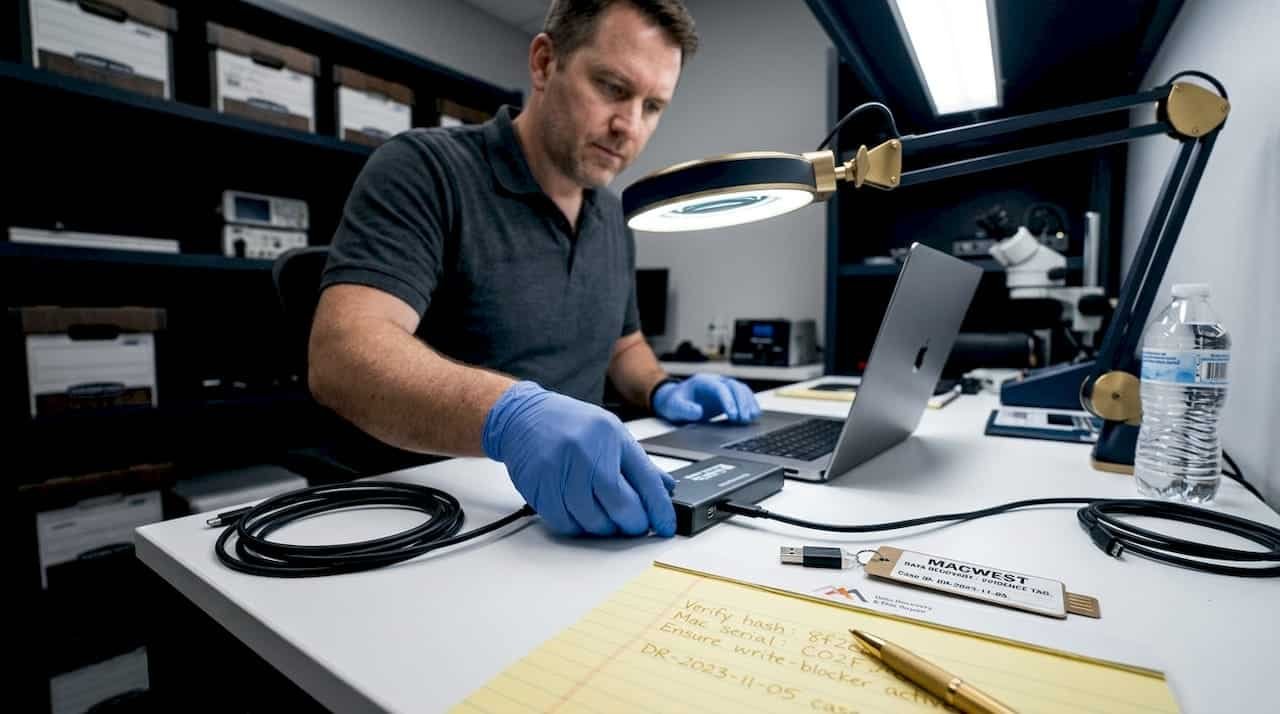
Drawing from years of field experience, here is what our Los Angeles forensic recovery team sees that most Apple users overlook, and what most recovery guides fail to mention.
The single most costly mistake we see is delay combined with overconfidence in consumer software. A client brings in a MacBook two weeks after the data loss event, having run three different recovery applications on it in the meantime. Each of those applications wrote temp files to the drive, potentially overwriting exactly the sectors containing the deleted data. TRIM has had two weeks to clear blocks. The chances of full recovery drop dramatically with every passing hour, and consumer tool activity accelerates that decline.
The second misconception is that Apple’s encryption is simply a password problem. Users assume that if they know their login credentials, any recovery tool can access their data. What they don’t account for is that T2 and M-series devices bind the decryption key to the specific hardware. A logic board failure means the key is potentially inaccessible regardless of credentials. This is not a limitation that can be solved with software. It requires physical board repair, often at the microsolder level, to restore key access before any data retrieval can begin. Our expert MacBook Pro guidance covers these hardware-level realities in detail.
The third overlooked reality is that forensic recovery requires documentation from the first moment, not as an afterthought. If you anticipate any legal use for recovered files, the recovery process itself must be documented with hash verification at each step, proving the data was not altered between the source and the final output. That documentation cannot be created retroactively. Choosing a forensic-capable provider from the start is the only way to preserve that option.
Finally, local proximity in Los Angeles matters more than most clients initially realize. Emergency same-day service, in-person chain-of-custody transfer, and direct consultation with the technician handling your case are practical advantages that a remote or mail-in service simply cannot match when data and evidence timelines are critical.
Connect with Los Angeles forensic data recovery professionals
If you’re facing lost data and want expert help in LA, here’s where to connect with qualified forensic recovery specialists.
Macwest Data Recovery and Mac Repair has served Los Angeles clients since 2006, handling everything from straightforward file retrieval to complex forensic cases involving encrypted Apple Silicon devices and damaged storage arrays.
Whether you’re dealing with a physically damaged drive, a failed logic board, or data loss following liquid exposure, our team applies the right methodology for your specific situation. Start with our hard drive recovery in Los Angeles page to understand your options for mechanical and SSD storage. Review our Mac recovery methods for LA users for a step-by-step breakdown of how we approach different loss scenarios. And if your device has suffered water or liquid damage, our Apple liquid damage recovery service addresses the corrosion and board damage that often accompanies these events. Do not wait and risk further data loss. Contact Macwest today for a free evaluation.
Frequently asked questions
Can deleted files always be recovered from a Mac?
No. Secure overwrite and SSD TRIM can permanently eliminate deleted data, particularly on newer Apple devices where TRIM runs aggressively and continuously.
Is forensic data recovery needed for legal cases?
Yes. Forensic recovery preserves metadata, file integrity, and chain-of-custody documentation that courts, attorneys, and compliance officers require for evidence to be admissible.
Can standard recovery tools work for encrypted Apple drives?
No. T2/M-series encryption ties decryption keys to the specific hardware, meaning standard tools cannot access encrypted data without board-level repair and specialized forensic techniques.
Are forensic methods slower or more expensive than consumer recovery?
Yes. Verified forensic imaging is slower and more costly than consumer tools, but it produces legally defensible evidence and documentation that no consumer application can replicate.
How do APFS snapshots help with data recovery?
APFS snapshots allow forensic technicians to roll back a volume to an earlier point in time, recovering files that existed before a deletion or corruption event occurred on the Mac.